Enable SSO with Okta OIDC
Single Sign-On (SSO) is an authentication method that enables users to log in to multiple applications and websites with one set of credentials. SSO uses certificates to establish and maintain a trust relationship between the Service Provider (SP) and an Identity Provider (IdP). Palette supports SSO based on either the Security Assertion Markup Language (SAML) or OpenID Connect (OIDC).
The following steps will guide you on how to enable Palette SSO with Okta Workforce Identity Cloud based on OIDC.
Prerequisites
-
For Okta OIDC to work correctly with Palette, you must enable HTTPS and configure TLS.
-
You need to have either a free or paid subscription with Okta. Okta provides free developer subscriptions for testing purposes.
-
If you want to use the same Okta application for OIDC-based SSO into your Kubernetes cluster itself, you need to install kubelogin on your local workstation to handle retrieval of access tokens for your cluster.
Okta with OIDC
Create the Okta Application
-
Log in to your Okta Admin console and navigate to Applications --> Applications. Click the Create App Integration button.
infoYour Okta login URL has the following format,
https://{your-okta-account-id}-admin.okta.com/admin/getting-started. Replace{your-okta-account-id}with your Okta account ID. -
In the screen that opens, select OIDC - OpenID Connect` for the sign-in method, then select Web Application for the application type. Then click Next.
-
The following screen allows you to configure the new Web App Integration. On the App integration name field, change the name from
My Web ApptoSpectro Cloud Palette OIDC. If desired, you can also upload a logo for the application. Leave the Grant type to its default value - Authorization Code.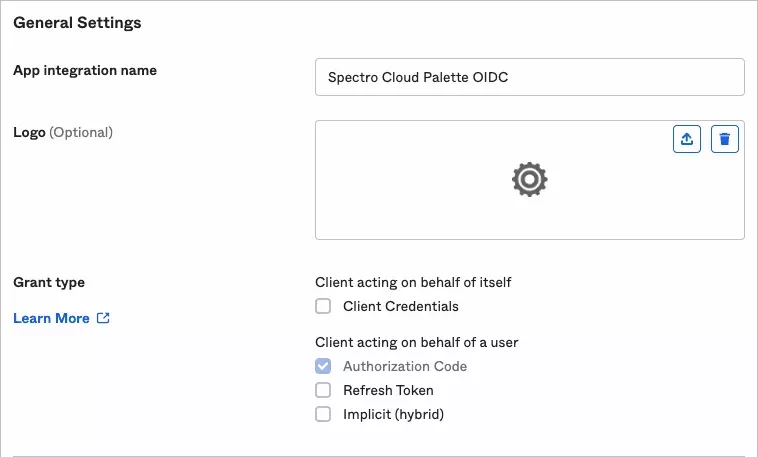
-
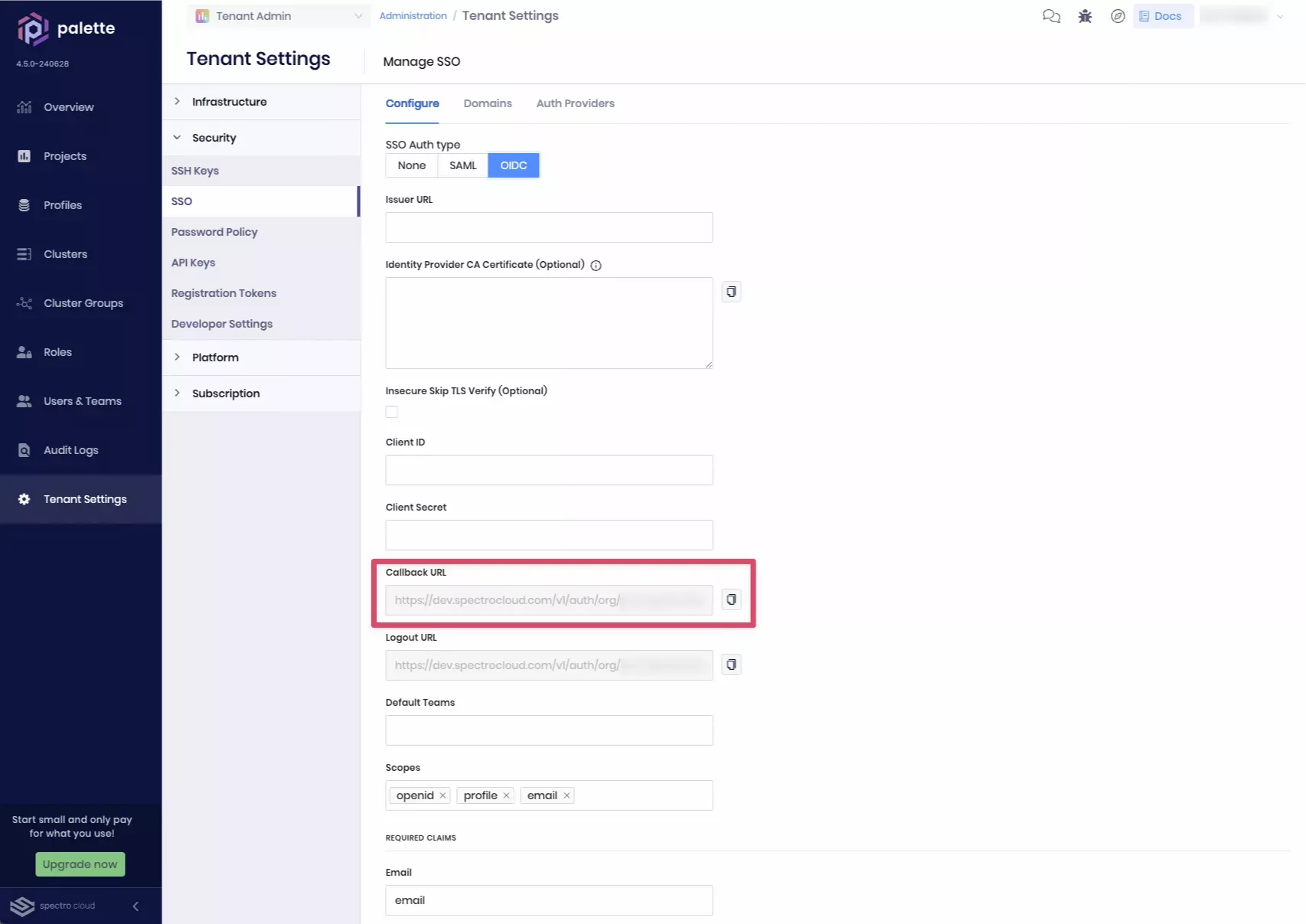
Open a web browser and navigate to your Palette subscription. Navigate to Tenant Settings --> SSO and click OIDC. Click the button next to Callback URL to copy the value to the clipboard.
-
Switch back to your Okta Admin console and paste the copied value into the Sign-in redirect URIs field, replacing the existing value:

-
Switch back to Palette in the web browser and click the button next to Logout URL to copy the value to the clipboard.
-
Switch back to your Okta Admin console and paste the copied value into the Redirect URI field, then click Add to add it to the list:
-
These two redirect URIs are required for SSO to work with Palette. You can also add additional redirect URIs. The URIs in the table below are useful when you want to use Okta for OIDC authentication into your Kubernetes clusters.
URL Type of Access http://localhost:8000Using kubectl with the kube-login plugin from a workstation. https://console.spectrocloud.com/v1/shelly/oidc/callbackUsing the web-based kubectl console. https://<fqdn_of_k8s_dashboard>/oauth/callbackUsing OIDC authentication into Kubernetes Dashboard. -
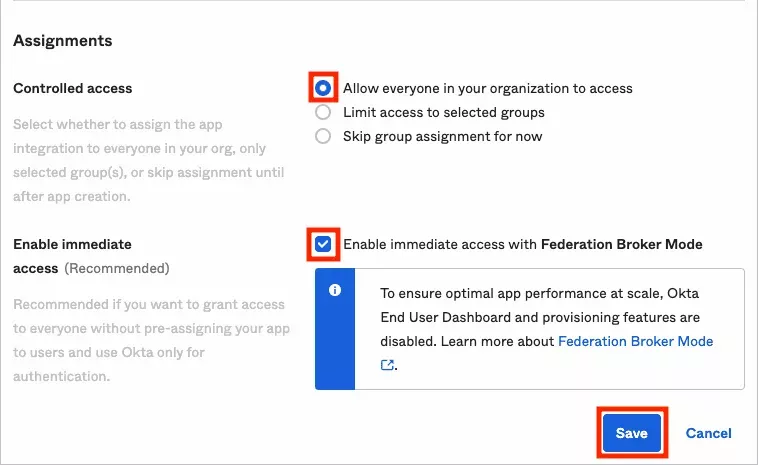
When you have completed entering redirect URIs, scroll down to the Assignments section and section and select Allow everyone in your organization to access. Leave the Enable immediate access with Federation Broker Mode option enabled and click Save.
-
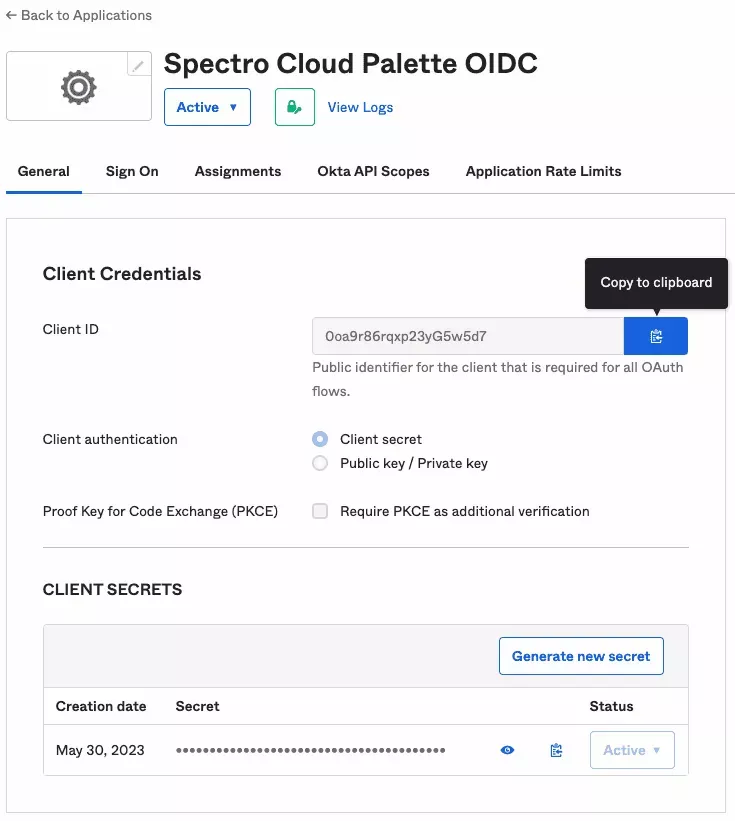
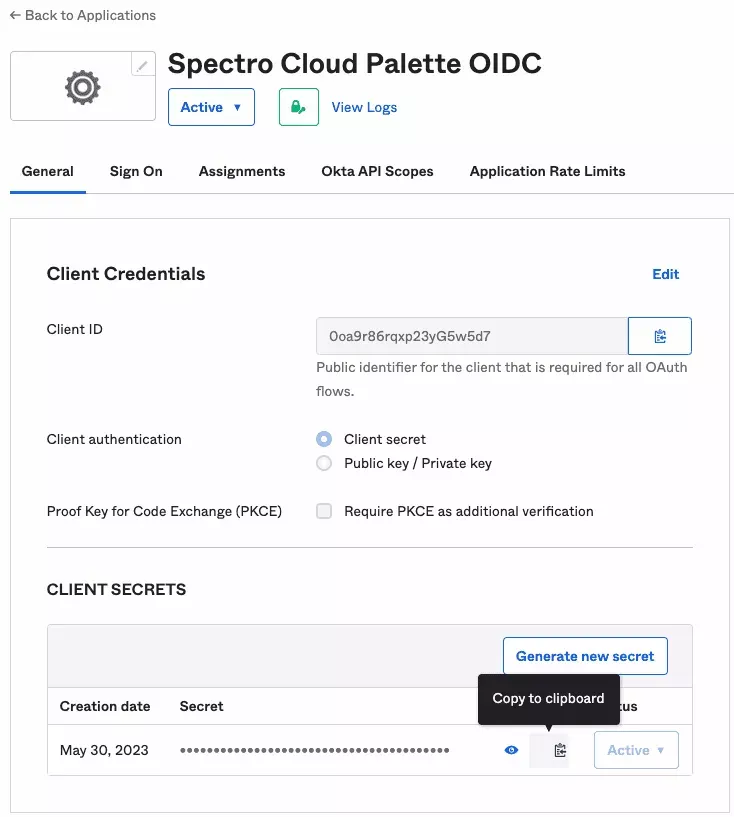
You have now created the Okta Application! Next, you need to retrieve the Client ID and Client Secret information, which you will use in the following steps. You should have landed on the General tab of your Okta Application. Click the Copy to clipboard button next to the Client ID to copy the secret value and save it somewhere. You will need this value for later.
-
Click the Copy to clipboard button next to the Client Secret to copy the secret value and save it. You will need this value for a later step.
Create an Okta Authorization Server
To ensure Okta issues OIDC tokens with the correct claims, you must create a custom Authorization Server. A custom Authorization Server is required to customize the authorization tokens issued by Okta so that they contain the necessary OIDC claims required by Palette and Kubernetes.
-
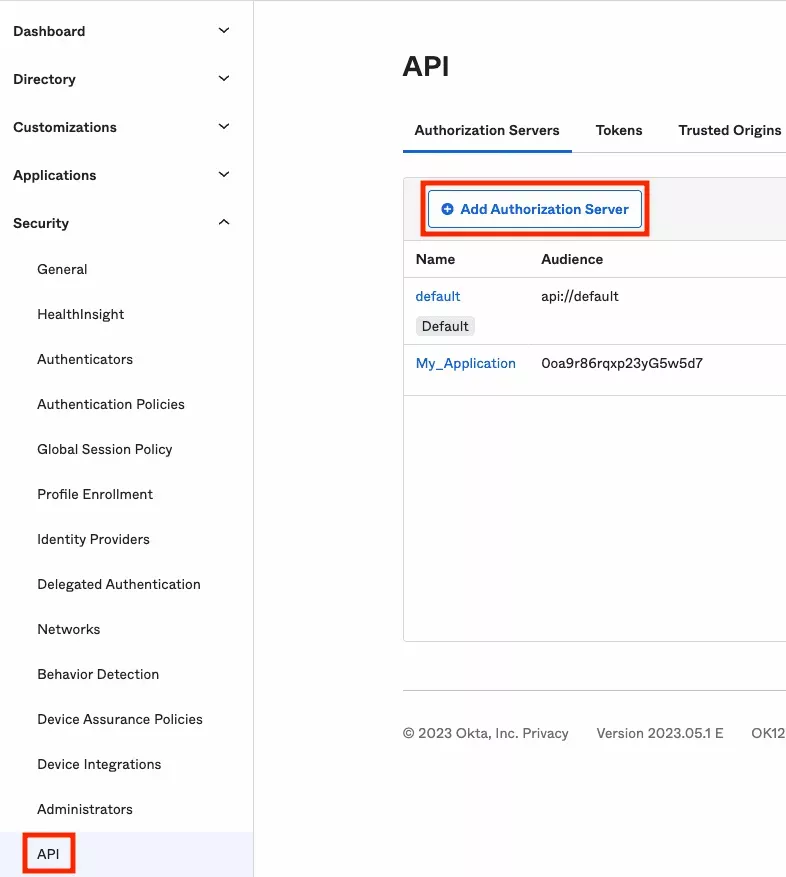
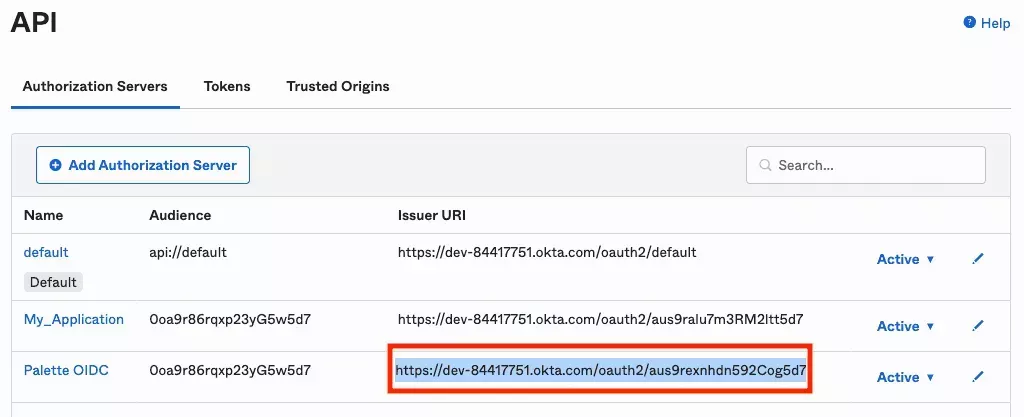
Navigate to Security --> API and on the Authorization Servers tab and click Add Authorization Server.
-
Enter a name for the server, for example
Palette OIDC. For the Audience field, enter the client identifier that you saved in step 10. Optionally provide a description. Then click Save. -
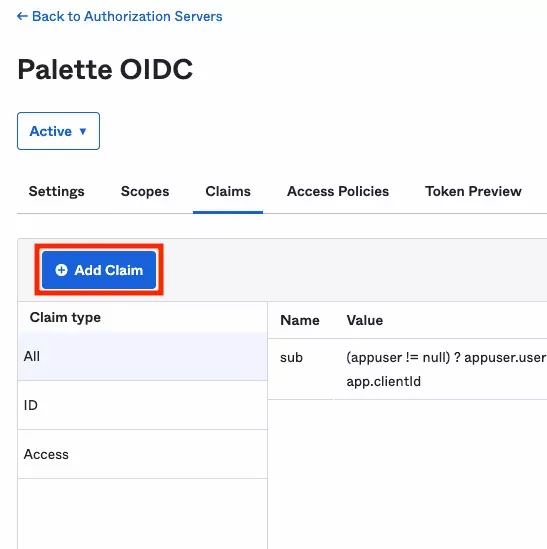
Navigate to the Claims tab and click Add Claim.
-
Enter the required information from the following tables below and click Create. Use this flow to create three claims in total. First, create two claims for the user information.
Claim Name Include in token type Value Type Value Disable claim Include In u_first_nameID Token (Always) Expression user.firstNameUnchecked Any scope u_last_nameID Token (Always) Expression user.lastNameUnchecked Any scope -
Next, create a claim for group membership. The example below will include the names of any groups that the Okta user is a member of, that start with
palette-, in thegroupsclaim of the ticket. For Palette SSO, Palette will make the user a member of Teams in Palette that have the identical name.Claim Name Include in token type Value Type Filter Disable claim Include In groupsID Token (Always) Groups Starts with: palette-Unchecked Any scope 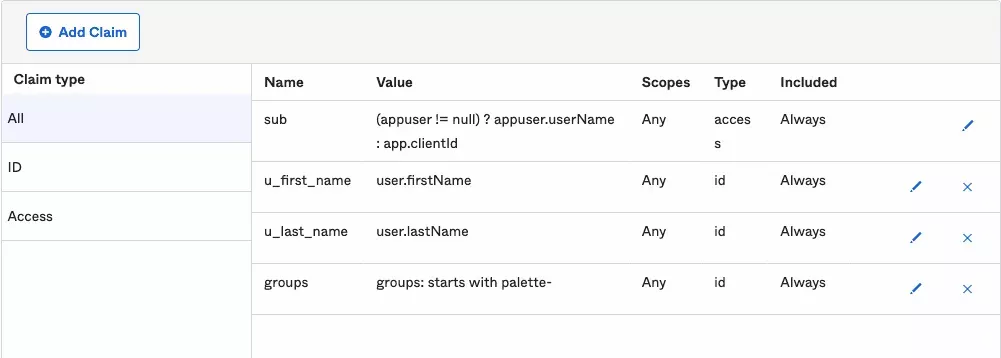
-
Click on <-- Back to Authorization Servers at the top of the page to navigate back to the list of all servers. The authorization server you created is displayed in the list. Select the Issuer URI shown and copy it to the clipboard. Save this value as you will use it in a later step.
-
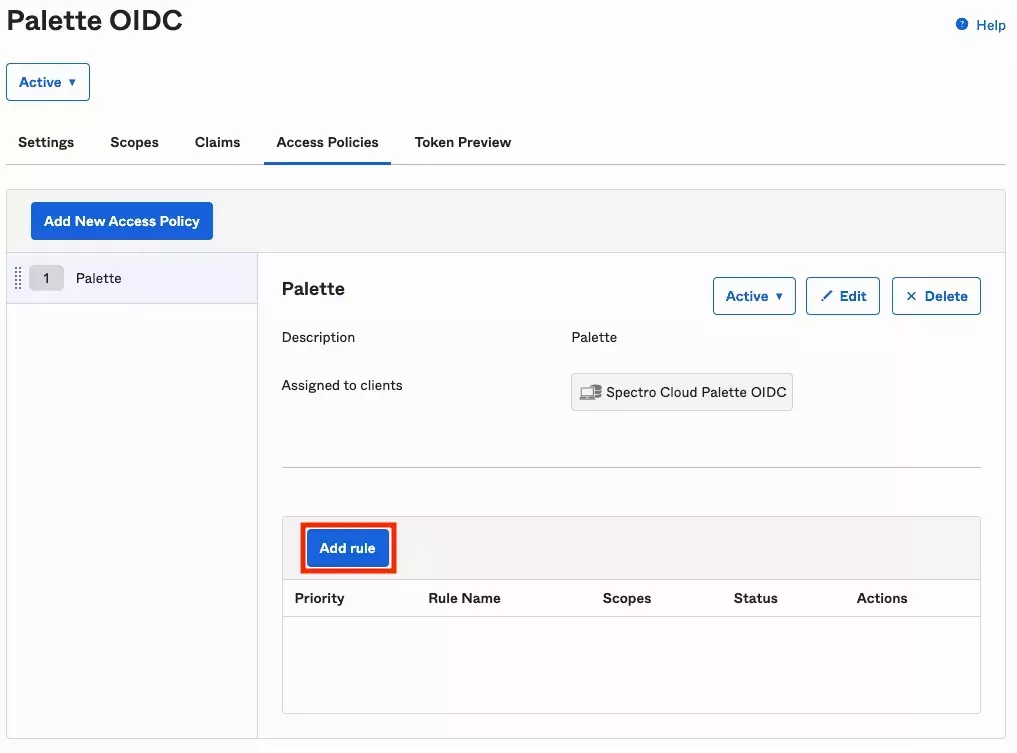
Navigate to the Access Policies tab and click Add Policy.
-
Set the Name and Description fields to
Palette, then change the Assign to option to the Okta Application you created in step three -Spectro Cloud Palette OIDC. Type in the first few characters of the application name and wait for a search result to come up that you can click on. -
Click the Add rule button to add a rule to this Access Policy:
-
Set the Rule Name to
AuthCode. Then deselect all Grant types but one, only leaving Authorization Code selected. Then click Create Rule.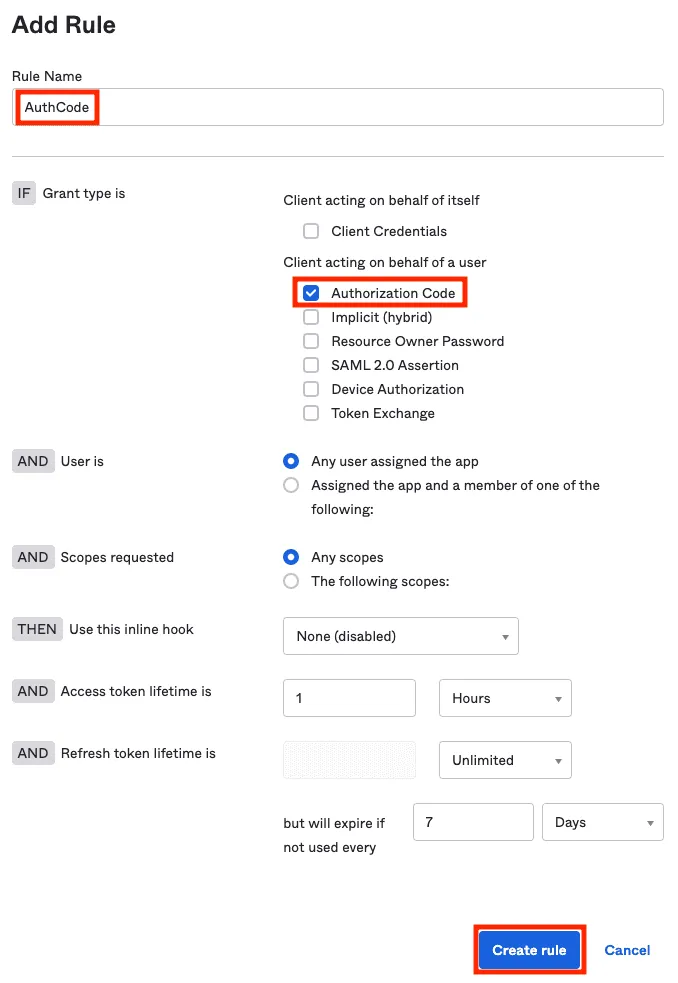
You have now completed all configuration steps in Okta.
Enable OIDC SSO in Palette
-
Open a web browser and navigate to your Palette subscription. From the left Main Menu, select Tenant Settings and click on SSO. Next click on OIDC. Enter the following information.
Parameter Value Issuer URL The Issuer URI that you saved in step 15. Client ID The client identifier that you saved in step 10. Client Secret The shared secret that you generated in step 11. Default Teams Leave blank if you don't want users without group claims to be assigned to a default group. If you do, enter the desired default group name. If you use this option, be careful with how much access you assign to the group. Scopes Keep openid,profileandemailas the default.Email Keep emailas the default.First Name Set this to u_first_name.Last Name Set this to u_last_name.Spectro Team Keep groupsas the default.
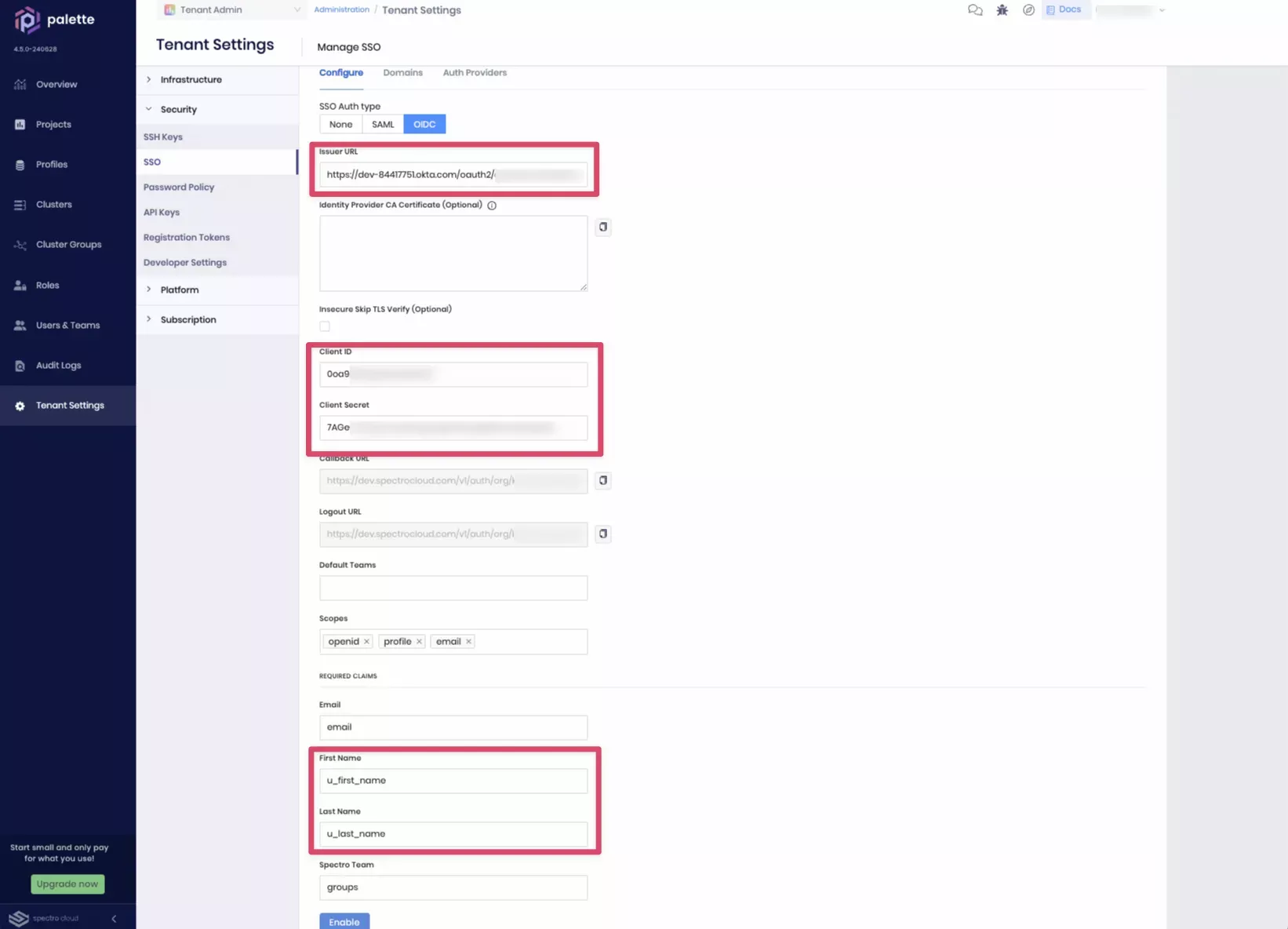
- When all the information has been entered, click Enable to activate SSO. You will receive a message stating OIDC configured successfully.
Create Teams in Palette
The remaining step is to create teams in Palette for the group that you allowed to be passed in the OIDC ticket in Okta,
and give them the appropriate permissions. For this example, you will create the palette-tenant-admins team and give
it Tenant Admin permissions. You can repeat this for any other team that you have a matching Okta group for.
-
Open a web browser and navigate to your Palette subscription. Navigate to Tenant Settings --> Users & Teams --> Teams tab, and click + Create Team.
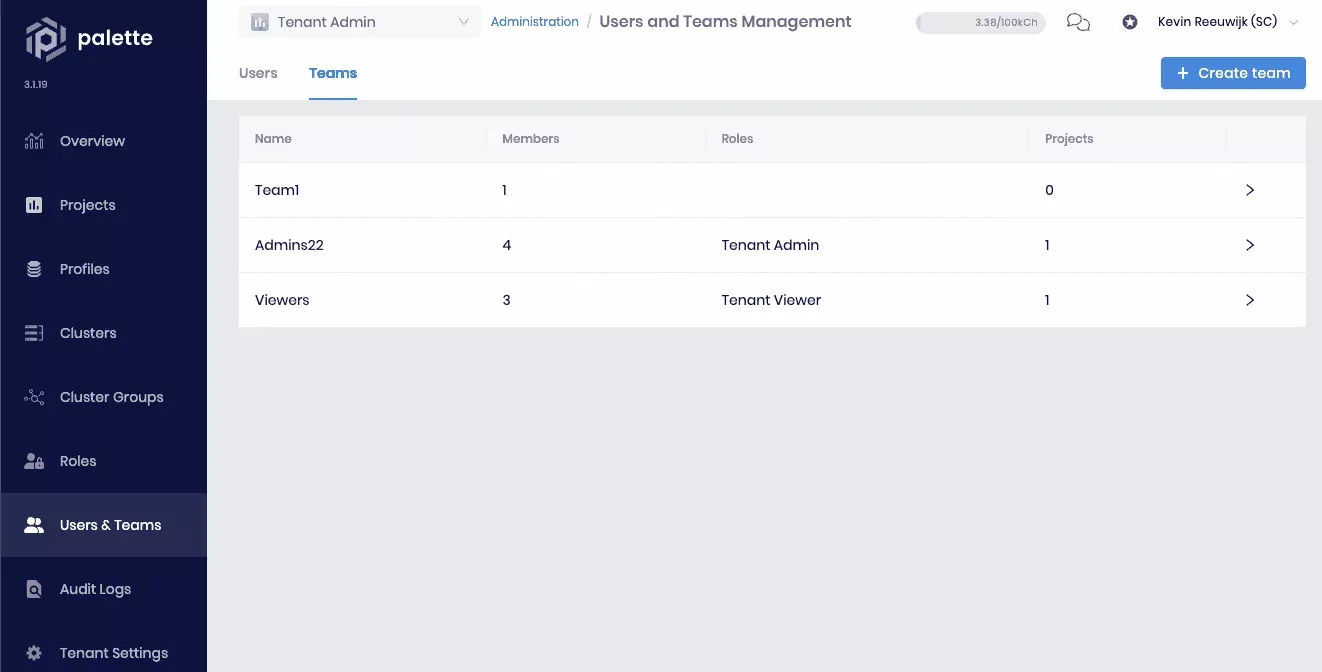
-
Specify
palette-tenant-adminsin the Team name field. You don't need to set any members now, as this will happen automatically from the SSO. Click Confirm to create the team. -
The list of teams displays again. Select the newly created palette-tenant-admins team to review its details. To give this team administrative access to the entire tenant and all the projects in it, assign the Tenant Admin role. Select Tenant Roles and click + Add Tenant Role:
-
Click on Tenant Admin to enable the role. Click Confirm to add the role.
You will receive a message stating Roles have been updated. Repeat this procedure for any other teams while ensuring they are given the appropriate access permissions.
-
Click the X next to Team Details in the top left corner to exit this screen.
You have now successfully configured Palette SSO based on OIDC with Okta.
Validate
-
Log in to Palette through SSO as a user that is a member of the
palette-tenant-adminsgroup in Okta to verify that users are automatically added to thepalette-tenant-adminsgroup in Palette. If you're still logged into Palette with a non-SSO user, log out by selecting Logout in the User Drop-down Menu at the top right. -
The Palette login screen now displays a Sign in button and no longer presents a username and password field. Below the Sign In button, there is an SSO issues? --> Use your password link. This link can be used to bypass SSO and log in with a local Palette account in case there is an issue with SSO and you need to access Palette without SSO. Click on the Sign in button to log in via SSO.
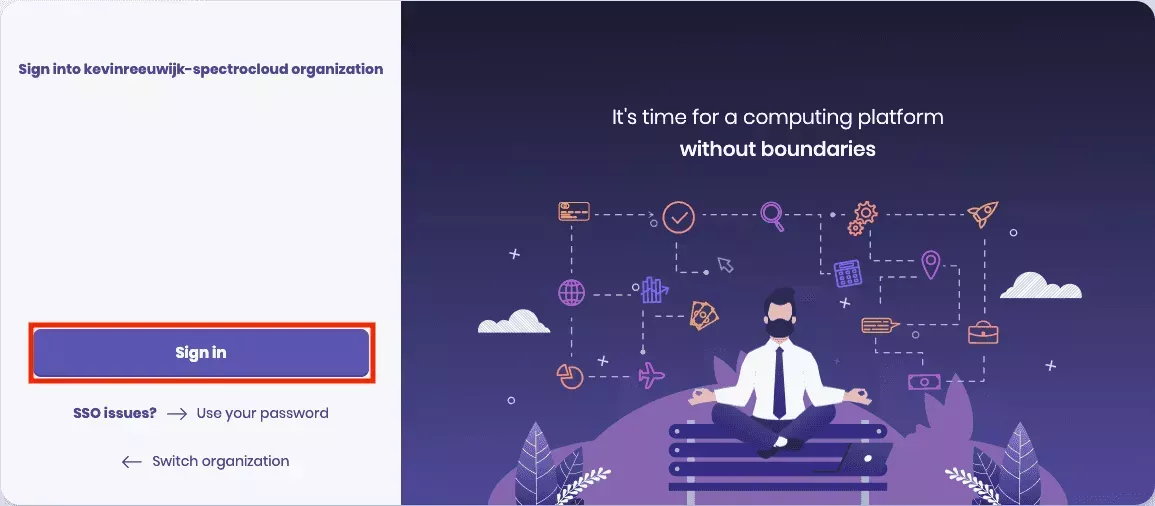
-
If this is the first time you are logging in with SSO, you will be redirected to the Okta login page. Depending on your organization's SSO settings, this could be a simple login form or require MFA (Multi-Factor Authentication).
infoMake sure you log in as a user that is a member of the
palette-tenant-adminsgroup in Okta. Once authenticated, you will automatically be redirected back to Palette and logged into Palette as that user. -
You are now automatically added to the
palette-tenant-adminsteam in Palette. To verify, navigate to the left Main Menu, select Tenant Settings --> Users & Teams --> Teams tab. Click the palette-tenant-admins team and view the team members section.