Spectro Proxy
Spectro Proxy is a pack that enables the use of a reverse proxy with a Kubernetes cluster. The reverse proxy allows you to connect to the cluster API of a Palette-managed Kubernetes cluster in private networks or clusters configured with private API endpoints. The reverse proxy managed by Spectro Cloud is also known as the forward reverse proxy (FRP).
The reverse proxy has a server component and a client component. The reverse proxy server is publicly available and managed by Spectro Cloud. The client is deployed inside your Palette-managed Kubernetes cluster and connects to the reverse proxy server. When you add the Spectro Proxy pack to a cluster profile, a couple of things happen:
-
Palette injects the reverse proxy server's SSL certificate into the cluster. This allows the cluster to trust the reverse proxy server.
-
The kubeconfig file is updated with the reverse proxy address instead of pointing directly to the cluster's API address. The following is an example of a kubeconfig file where the
serverattribute points to the reverse proxy.apiVersion: v1
clusters:
- cluster:
certificate-authority-data: LS......
server: https://cluster-61a578b5259452b88941a1.proxy.spectrocloud.com:443
name: example-server
contexts:
# The remainder configuration is omitted for brevity. -
Any requests to the Kubernetes API server, such as kubectl commands, will be routed to the reverse proxy. The reverse proxy forwards the request to the intended client, which is the cluster's API server. The cluster's API server authenticates the request and replies with the proper response.
You can attach this pack to a cluster profile. For more information, refer to Cluster Profiles. The pack installs the Spectro Proxy client in the workload clusters and configures the cluster's API server to point to a managed proxy server.
This pack can be combined with the Kubernetes Dashboard or Spectro Kubernetes Dashboard packs.
To learn more about exposing the Spectro Kubernetes Dashboard, check out the Spectro Kubernetes Dashboard guide.
Network Connectivity
The host cluster's network configuration defines who can access the host cluster from a network perspective. If a user is in the same network as the cluster, the user may be able to access the host cluster without needing a forward proxy. However, if the user is on a different network, the host cluster's network configuration may limit the user's ability to connect to the host cluster and may require the use of a forward proxy.
The Spectro Proxy pack does not support Edge deployments in airgapped environments where the Edge host does not have outbound access to the internet.
From a network configuration perspective, a cluster can be in a private or a public network. Host clusters deployed in a network that does not allow inbound internet access are considered private. Whereas the clusters deployed in a network with both inbound and outbound access to the internet are considered public. The following are the three possible network connectivity scenarios:
-
The cluster and the user are in the same private network.
-
The cluster and the user are in different private networks.
-
The cluster is in a public network.
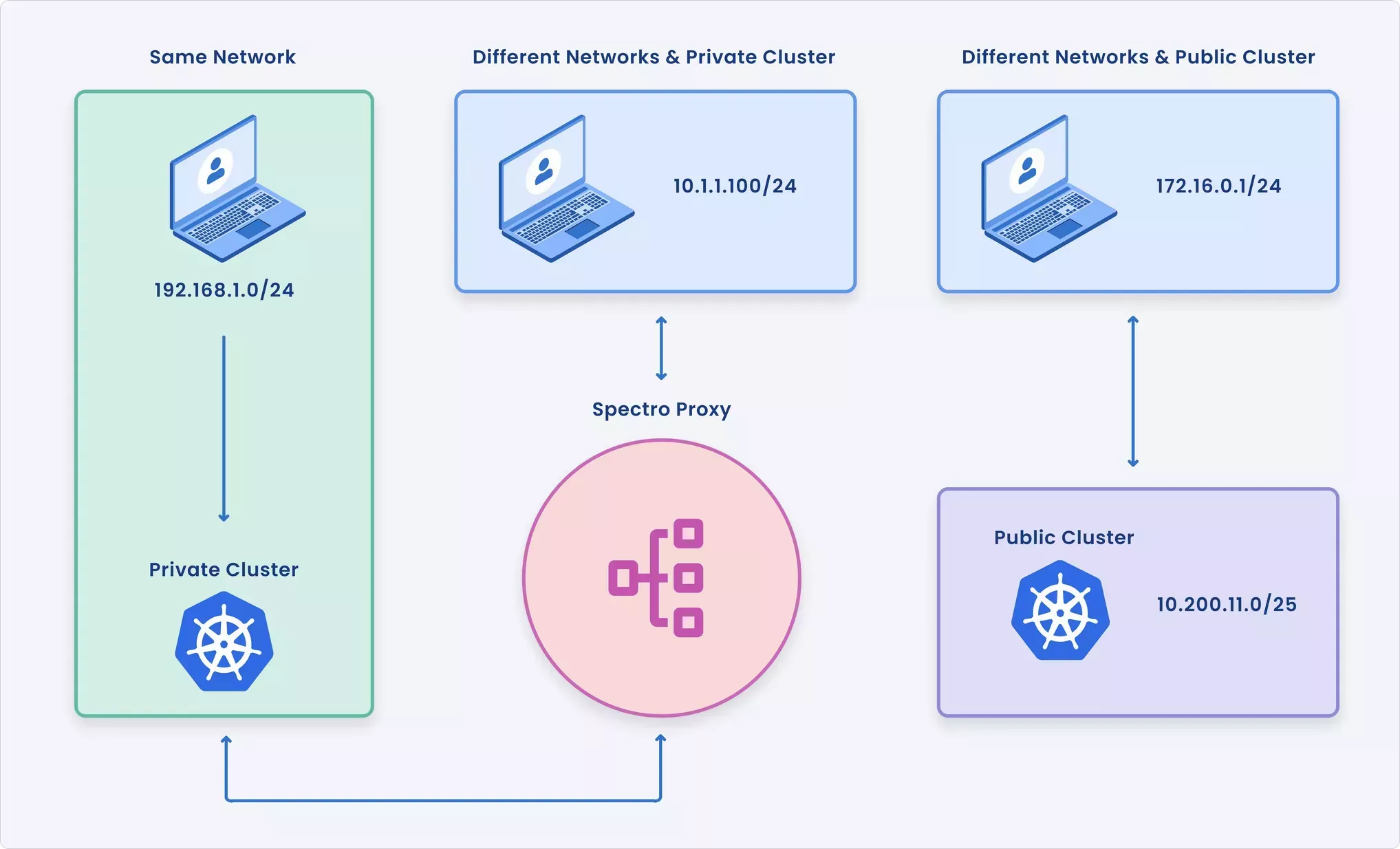
The following table summarizes the network connectivity requirements for each scenario and whether the Spectro Proxy is required.
| Scenario | Description | Requires Spectro Proxy? |
|---|---|---|
| Private cluster in the same network | The cluster is deployed with a private endpoint, and the user is also in the same network. | ❌ |
| Private cluster in a different network | The cluster is deployed with a private endpoint, and the user is in a different network. | ✅ |
| Public cluster in a different network | The cluster is deployed with a public endpoint, and the user is in a different network. | ❌ |
To learn more about how the Spectro Proxy interacts with clusters in a public or private network environment and when the Spectro Proxy is required, select the tab that matches your use case.
- Private Cluster in Different Network
- Private Cluster in Same Network
- Public Cluster
Networks labeled as private do not allow inbound internet access. Inbound network requests to the network are allowed only if the connection originated from the internal network. If you are in a different network than the cluster, you can connect to the cluster's API server through the Spectro Proxy. The Spectro Proxy allows you to connect to the cluster's API server although you are not in the same network as the cluster.
Users that are in a different network than the cluster require the Spectro Proxy server to connect to the cluster's API server. Otherwise, requests to the cluster's API server will fail due to a lack of network connectivity.
The Spectro Proxy client is installed by the Spectro Proxy pack. The client is deployed in the cluster and connects to the Spectro Proxy server. The Spectro Proxy server is a managed service that is publicly available and managed by Spectro Cloud. The Spectro Proxy server forwards the request to the cluster's API server. The cluster's API server authenticates the request and replies with the proper response.
The kubeconfig files generated for the host cluster are updated with the Spectro Proxy server's address. When you or other users issue a kubectl command, the request is routed to the Spectro Proxy server. The following is an example of a kubeconfig file where the SSL certificate and server address attribute point to the Spectro Proxy.
The following diagram displays the network connection flow of a user attempting to connect to a cluster with private endpoints. The user is in a different network than the cluster.
-
The user issues a kubectl command to the cluster's API server.
-
The request is routed to the Spectro Proxy server. The Spectro Proxy client inside the host cluster has an established connection with the cluster's API server.
-
The Spectro Proxy server forwards the request to the cluster's API server located in a different network. The cluster's API server authenticates the request and replies with the proper response.
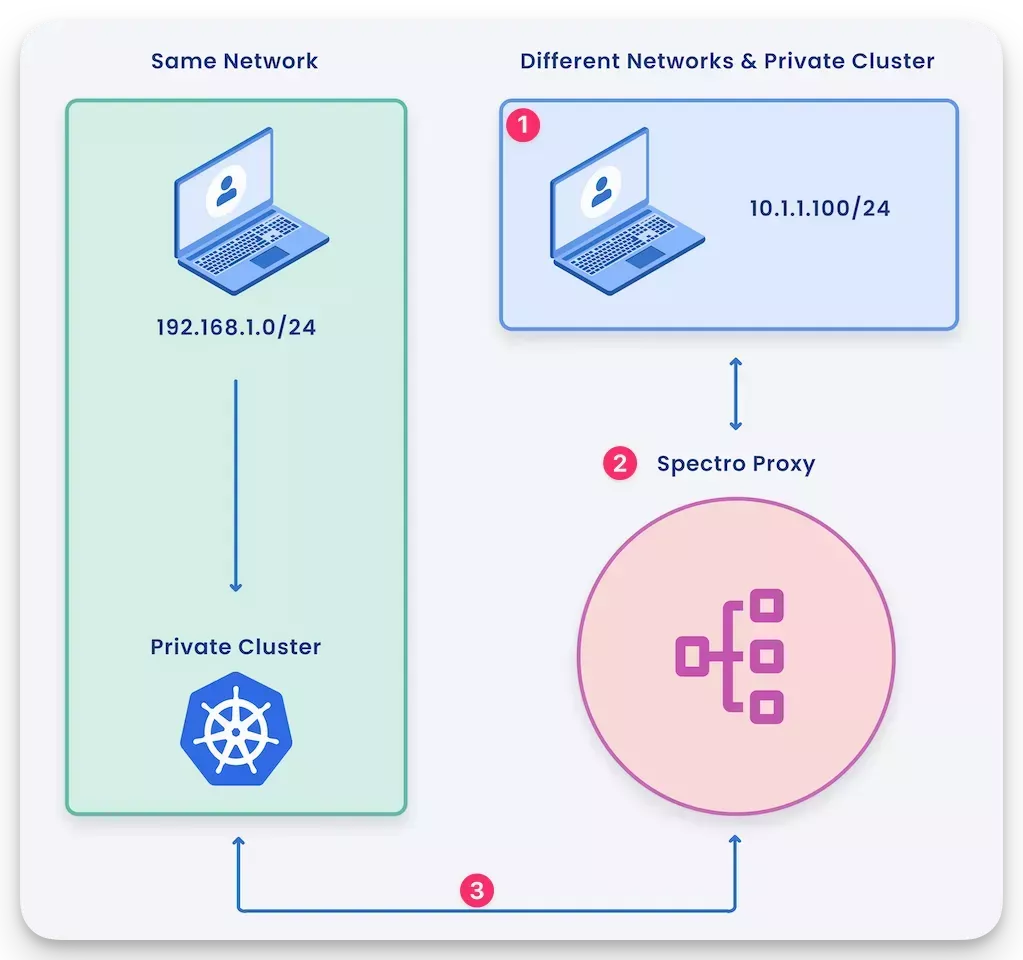
Depending on what type of infrastructure provider you are deploying the host cluster in, you may have to specify the Spectro Proxy server's SSL certificate in the Kubernetes cluster's configuration.
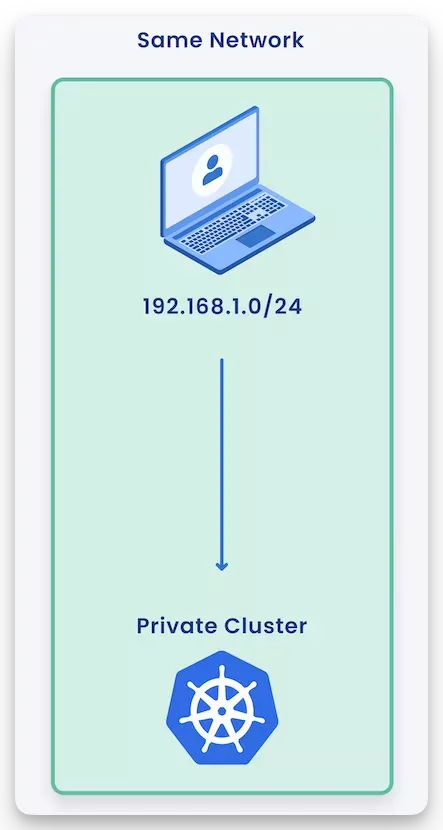
Networks labeled as private do not allow inbound internet access. Inbound network requests to the network are allowed only if the connection originated from the internal network. If you are in the same network as the cluster, you can connect directly to the cluster's API server. The term "same network" means that from a network perspective, requests can reach the cluster's API server without having to traverse the internet.
Users in the same network as the cluster do not require the Spectro Proxy server to connect to the cluster's API server.
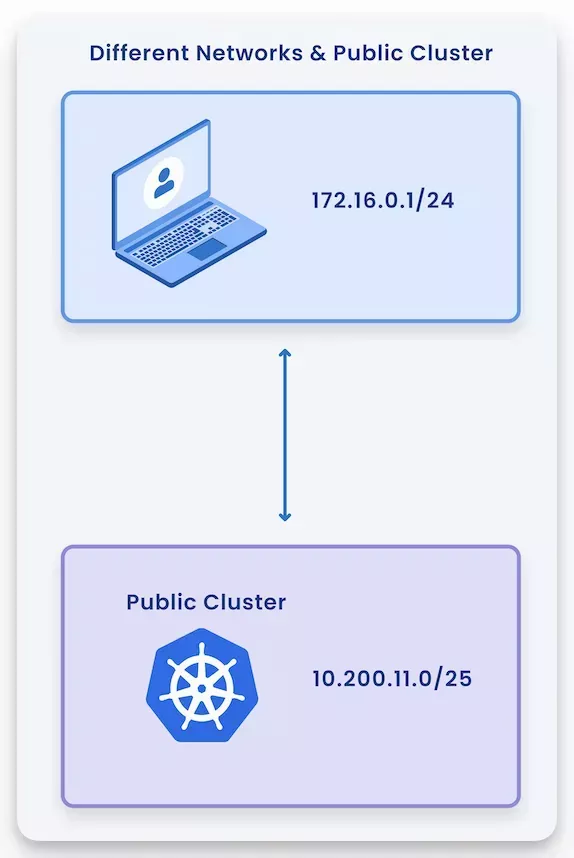
Clusters deployed in a network with both inbound and outbound access to the internet are considered public.
Clusters deployed in a public network do not require the Spectro Proxy to connect to the cluster's API server.
When a cluster has public endpoints, you can query the cluster's Kubernetes API server from any network with internet access. The following diagram displays the network connection flow of a user attempting to connect to a cluster with public endpoints. Any user with access to the internet can connect to the cluster's API server.
Versions Supported
- 1.5.x
- 1.4.x
- 1.3.x
- 1.2.x
To use this pack, you have to add it to your cluster profile. You can also add the Spectro Proxy pack when you create the cluster profile. Check out the Create Cluster Profile guide to learn more about cluster profile creation.
The kubeconfig file generated for the host cluster is updated with the Spectro Proxy server's address. Refer to the Access Cluster with CLI guide to learn how to download the kubeconfig file and access the cluster.
If this pack is added as a Day-2 operation, meaning not during the cluster creation process, you will have to re-download the kubeconfig file to pick up the new configuration changes. This will also result in the Kubernetes control plane nodes getting repaved.
To use this pack, you have to add it to your cluster profile. You can also add the Spectro Proxy pack when you create the cluster profile. Check out the Create Cluster Profile guide to learn more about cluster profile creation.
The kubeconfig file generated for the host cluster is updated with the Spectro Proxy server's address. Refer to the Access Cluster with CLI guide to learn how to download the kubeconfig file and access the cluster.
Be aware that if this pack is added as a Day-2 operation, meaning not during the cluster creation process, you will have to re-download the kubeconfig file to pick up the new configuration changes. This will also result in Kubernetes control plane nodes getting repaved.
To use this pack, you have to add it to your cluster profile. You can also add the Spectro Proxy pack when you create the cluster profile. Check out the Create Cluster Profile guide to learn more about cluster profile creation.
The kubeconfig file generated for the host cluster is updated with the Spectro Proxy server's address. Refer to the Access Cluster with CLI guide to learn how to download the kubeconfig file and access the cluster.
Be aware that if this pack is added as a Day-2 operation, meaning not during the cluster creation process, you will have to re-download the kubeconfig file to pick up the new configuration changes. This will also result in Kubernetes control plane nodes getting repaved.
To use this pack, you have to add it to your cluster profile. You can also add the Spectro Proxy pack when you create the cluster profile. Check out the Create Cluster Profile guide to learn more about cluster profile creation.
The kubeconfig file generated for the host cluster is updated with the Spectro Proxy server's address. Refer to the Access Cluster with CLI guide to learn how to download the kubeconfig file and access the cluster.
Be aware that if this pack is added as a Day-2 operation, meaning not during the cluster creation process, you will have to re-download the kubeconfig file to pick up the new configuration changes. This will also result in Kubernetes control plane nodes getting repaved.
Troubleshooting
Troubleshooting scenarios related to the Spectro Proxy.
x509 Unknown Authority Error
If you encounter an x509 unknown authority error when deploying a cluster with the Spectro Proxy.
Unable to connect to connect the server: X509: certiticate signed by unknown authorit signed by
The workaround for this error is to wait a few moments for all the kubeconfig configurations to get propagated to Palette. The Palette cluster agent sends the original kubeconfig to Palette, followed by the modified kubeconfig containing the reverse proxy settings. If you attempt to open up a web shell session or interact with cluster API during the initialization process, you will receive an x509 error. Once Palette receives the kubeconfig file containing the cluster's reverse proxy configurations from the cluster agent, the x509 errors will disappear.
Terraform
You can reference the Spectro Proxy pack in Terraform with a data resource.
data "spectrocloud_registry" "public_registry" {
name = "Public Repo"
}
data "spectrocloud_pack_simple" "spectro-proxy" {
name = "spectro-proxy"
version = "1.5.3"
type = "operator-instance"
registry_uid = data.spectrocloud_registry.public_registry.id
}